Security vs. Privacy
Author’s Note
This post is my analysis of security vs. privacy which I have submitted to Edinburgh Napier University in fulfillment of my masters programme.
Abstract
The purpose of this post is to investigate the relationship between security and privacy, as well as to investigate issues of governance that may arise from supporting privacy in an organisation. In addition to this investigation, privacy and its rise in importance are defined. The definition of privacy and study is accomplished by reviewing, comparing, and critically analysing recently published academic literature. This post does not focus on a specific sector within the IT industry but instead focuses on privacy as a subject.
The outcome of defining privacy found that it owns control over one’s personal data. Privacy and security are correlated with each other; however, they can be two separate entities. It is recognised that security has a positive correlation with privacy. It is identified that the greatest challenge to information security governance is the awareness and training of employees towards ethical and legal requirements as well as the company’s policies.
Introduction
In the German Democratic Republic (GDR) when the Ministry for State Security (MFSS) (German: Ministerium für Staatssicherheit, MfS) was active, people were left distraught, and there was a lingering feeling of an open-air prison (Hardach, 2019). Moreover, the MfSS engrained traumatic experiences into the victims of MFSS operation (Neuendorf, 2017). MfSS operation was very offensive, including but not limited to undercover spies, intercepting mail, tapping phone lines, placing microphones in homes (Neuendorf, 2017). In 2013, Snowden leaked the National Security Agency’s (NSA) intent of mass surveillance in cooperation with other corporations, codenamed PRISM (Berghel, 2013; Landau, 2013). The PRISM project included monitoring of information technology such as but not limited to e-mails, chat (video/voice), stored data, VoIP (Greenwald & Macaskill, 2013). Privacy used to be relatively easy to maintain before the information age, as communications did not take place over e-mail, text messages, or social media pages (Schneier, 2013). Now that communications typically go through a third party, they are subject to interception and storage without people realising it in the same way they realised surveillance from the MFSS.
Article 8 of the European Human Convention Rights (EHCR) of 1950 establishes a legal right by stipulating that everyone has the right to respect for their private life and their homes. Moreover, it prevents public authorities from breaking one’s right to respect for their private life unless it is in the interest of but not limited to national security or public safety. The overarching issue is that there used to be no centralised governing body to ensure that organisations are complying with privacy policies. In April 2015, the FCC issued a $25 million fine to AT&T for mistreating customer information in a data breach. While the FCC was acting in the interest of privacy, they had received criticism for enforcing new privacy definitions without public notice (Ruckman & Dhaliwal, 2015). The introduction of the General Data Protection Regulation (GDPR) / Data Protection Act (DPA) 2016 attempts to overcome these issues. GDPR became enforceable, and the central governing regulation limited to European nationals on May 25, 2018.
Defining Privacy
Dictionary definitions of privacy fail to consider the subjective element of privacy; privacy will be defined in separate ways by different demographics depending on experiences. Furthermore, dictionary definitions can also suggest a physical separation which is not applicable in the digital world. Privacy can also be considered to be a very “chameleon” type of word; adapting to the situation for which it is used. The definition of privacy does not only change between different demographics, but it can change within a single demographic with separate people having different previous experiences. For an item to be confidential, it must be private or a secret to those who are unauthorised to the item. The instant that secrets are exposed to unauthorised persons the secret is no longer confidential. Unlike confidential, privacy is used in a broad application of cases where it begins to lose a concrete meaning that it might once have had (Solove, 2006).
There are cases in which it would make sense to share private information with select people such as healthcare personnel. The Health Insurance Portability and Accountability Act (HIPAA) 1996 enforces standards in the USA which mandate the health care sector to protect the confidentiality and security of customers’ health data. The HIPAA attempts to ensure that privacy is not lost; the data sharing between medical practices is performed in a controlled manner – assuming there are no malicious actors. However, if people lose control over their private information, they will claim that there has been a violation of their privacy.
Being in a state of privacy can be described as owning the control of one’s private information or over information worth preserving (Orrù, 2017; Torra, 2017). In a networked world of today, many will publish a considerable amount of information about themselves through online platforms. That could happen through personal blogs or other social media personal profiles such as on Facebook or LinkedIn, among others. Knowing this, one could argue that shoulder surfing (the act of an adversary watching over a victim’s shoulder) is no longer a violation of privacy that it once was before computer technology and the internet became so widespread. If information is available online, why does it matter from where an adversary obtains the information? However, on the other hand, it is argued that shoulder surfing can still be a violation of privacy as people should hold control of what they publish about themselves online (Wiederhold, 2018). One can limit the amount of information gained about oneself by reducing the amount of sensitive information published online.
The Internet of Things (IoT) includes a myriad of devices ranging from mobile phones to car dash cameras, or smart devices (thermostats, smart speakers) within a household, the workplace and in public places. These all produce a large amount of data which can be collected and analysed by companies. The GDPR attempts to limit the processing of personal data through its principle that data collection must be lawful, fair, and transparent. This principle prevents companies such as Google or Amazon (among others) to permanently listen to, process, and analyse conversations through their smart speakers. Furthermore, it can prevent Apple or other smartphone manufacturers from analysing telemetry data such as location or camera information in an extended manner.
Security and Privacy
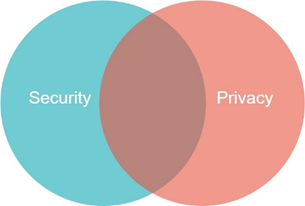
Security and privacy are often discussed together as a single entity. If information is private, then it must be kept securely and vice versa. However, there can be cases where security and privacy are not related. If a blog web application is compromised to promote an adversary’s agenda by defacing the website, the privacy of the users is not compromised. Alternatively, if one has private information openly published on a secure web application, the security is not compromised, but rather the privacy is lost. Figure 1 visually displays that security and privacy have an area in which they relate to each other; however, also depicts that there are areas which are unrelated to each other. Of course, security and privacy do have a positive correlation with each other; the more secure something is, the likelihood of privacy loss is reduced. Increased security leading to privacy is a principle known as Privacy by Design (PbD) (Torra, 2017). PbD should be incorporated throughout the whole product development process, however inherits the issue that there is no agreed standard for PbD implementation or best practices (Orrù, 2017).
Solove argues that there are four groups of harmful activities to privacy (Solove, 2006): (1) Information collection through surveillance. (2) Information processing through the aggregation of information. (3) Information dissemination used for distortion, and breaches confidentiality (4) Invasion, including intrusion and decisional interference. A more recent research paper by Orrù relating to data mining discusses four stages of data processing towards surveillance through a scenario of a public transport system (Orrù, 2017): (1) No data collection (2) Anonymous data collection which could be used to infer patterns. (3) Data profiling to identify habits. (4) Full surveillance using profiled data to make decisions. A side by side comparison of the two methodologies is seen in Table 1 below.
| Stage | (Solove, 2006) | (Orrù. 2017) |
| 1 | Information collection | No data collection |
| 2 | Information processing | Anonymous data collection |
| 3 | Information dissemination | Data profiling |
| 4 | Invasion | Full surveillance |
These approaches are similar in that the fourth stage is invasion / full surveillance. However, where these models differ is at the upper stages (3 and 4). Orrù suggests that anonymous data collection is not a breach of privacy, where Solove suggests that any data collection violates one’s privacy. Perhaps around the time of Solove’s paper, anonymous data collection had not been a prominent consideration. A significant factor to this change can be attributed to the GDPR, as the regulation does not apply to anonymised data.
An example of a stage 4 invasion / full surveillance could be how Cambridge Analytica bought information of Facebook users to analyse and profile user information. Referring back to the definition of privacy, the reason that this breached people’s privacy is because even persons who did not have an account with Facebook could have their data profiled if they browsed webpages associated with Facebook (Isaak & Hanna, 2018). Persons without a Facebook account lost control over personally identifiable information as they were included in data profiling. Stalla-Bourdillon’s raises an interesting point that in order for police or government agencies to protect the community, some level of privacy must be breached (Stalla-Bourdillon, 2014). For example, by use of data profiling and surveillance (stage 3 and 4 in Table 1) it could be possible to detect various (e.g. individual or mass) attacks before they occur. There is a difficult line which defines when surveillance is used to ensure community security (e.g. security cameras) or to exploit community data for security agencies’ own interests (e.g. terrorist detection and prevention).
Governance and issues supporting privacy
Information security governance can consist of many tasks, including but not limited to, creating policies, procedures, and guidelines. Information security management is tasked with ensuring that users are aware and are committed to the established policies, procedures, and guidelines. Governance ensures that the IT strategy of an organisation is aligned with the enterprise objectives (Carcary et al., 2016). Moreover, information security governance often ensures that the three properties of confidentiality, integrity, and availability (C.I.A.) are maintained (Carcary et al., 2016; Fazlida & Said, 2015). The greatest challenge posed to the governance of supporting privacy is ensuring that users are aware and committed to information security policies and processes within an organisation. This is because even if the information security technology is of the latest standard, humans can be subject to coercion or manipulation to undertake tasks which they otherwise should not. Alternatively, users could attempt to circumvent information security policies in an attempt to complete their tasks more quickly. However, if users get a false sense of security from the organisation, they could also begin to ignore security policies believing that the company will have other defences in place (D’Arcy & Greene, 2014). Frameworks such as ISO/IEC 27002:2013 and COBIT 5 could help to tackle the false sense of security, as there are chapters dedicated towards creating a positive security culture within the organization.
There are many frameworks that organisations could comply with, and the incentive to follow one is significant. Without the usage of frameworks, it is highly likely that business controls are loosely defined and that they are not designed correctly to suit the organisation (Rohn et al., 2016). Some example information security frameworks can be seen in Table 2 below.
| Framework Name | Aims of the framework |
| ISO 27001 – Information Security Management Systems – Requirements | Provide requirements for implementing organisational information security management systems (ISO/IEC, 2013). |
| ISO 27013:2015 – Guidance for integrated implementation of ISO/IEC 27001 | Helps to guide the integrated implementation of ISO/IEC 27001 (BS ISO, 2015). |
| ISO 29001:2011 – Privacy framework standard | Helps to implement a privacy framework (British Standards Institution, 2011). |
| Control Objectives for Information and Related Technologies (COBIT) | To provide an information technology governance framework, not exclusive to information security (von Solms, 2005). |
The mentioned frameworks in Table 2 all have the advantage that organisations can be audited against these frameworks by independent, authoritative organisations which will confirm that an organisation is complying with a certain level of the frameworks’ standards, according to a maturity model. A maturity model can be used to concretely state the extent of which controls are being complied to. Additionally, the maturity model can be used to tell upper management that there is a requirement for improvement. An example maturity model can be seen in Table 3 below (Rohn et al., 2016).
| Maturity Level | Description / Criteria of the maturity level |
| 5 – Optimized | Ongoing improvement towards the process to meet business objectives. IT is used to automate the workflow, providing tools to improve effectiveness. |
| 4 – Managed | Monitoring the compliance of the process is in place. Action is taken when necessary. |
| 3 – Defined | Procedures are standardized, documented and communicated. |
| 2 – Repeatable but intuitive | Procedures followed by employees, however there is no formal training or communication on procedures. |
| 1 – Ad hoc | Evidence the need, however there is no standardized procedure in place. |
| 0 – Non-existent | Lack of a process, or process fails to achieve its purpose |
In von Solms’s report, the COBIT and ISO 17799 frameworks had been compared (von Solms, 2005). ISO 17799 was released in 2005 and has since then been modified and became ISO 27002. Von Solms considers that COBIT is very good for explaining what information security is but is limited in explaining information security implementation (von Solms, 2005). However, the ISO 27002 standard can be a more useful framework for information security as it explains how controls could be implemented. The problem derived from this could be that as there are many frameworks that organisations could follow, selecting the most appropriate framework could be a challenge. Additionally, controls are not a set and forget solution, but instead, they must undergo ongoing review to assess their effectiveness. Moreover, compliance of controls must be assessed for example through a maturity model (Carcary et al., 2016; Rohn et al., 2016).
Further challenges could arise depending on the business location and the data subject information held. The GDPR/DPA 2016 mandates that all organisations which handle EU data subjects’ data regardless of location comply with the regulation (Vollmer, 2018a). While this is not necessarily an issue outright, organisations must consider the users that could be using their service and apply security processes appropriately.
Conclusions
This post focussed on defining privacy, comparing security vs privacy, and finally analysed issues that arise in supporting privacy within an organisation. It was found that privacy can be defined as owning control over one’s personal data. People are willing to share personal information for example during medical practice. However, one could be upset when confidentiality of such data is lost, more importantly, when control over the data is lost. When it comes to security vs privacy comparison, it was found that security has a positive correlation with privacy; privacy by design is implemented through fundamental/additional security controls. Four stages of data processing have been analysed regarding the loss of control over one’s data; breaching one’s privacy. It is found that government bodies undergo some level of privacy breach in the national interest for physical security. Finally, it was found that information security awareness and education is the greatest challenge for governance within an organisation. Select frameworks were compared against each other, identifying that different frameworks regarding information security have separate approaches towards accomplishing a similar task.
Further research could be to develop an information security framework which is tailored towards the GDPR/DPA 2016. It is an integral part of information security governance that the correct framework is selected which suits the organisation goals. There are many information security frameworks available (e.g. COBIT, ISO/IEC 27002, ISO/IEC 29100), and selecting the correct one helps to maximise efficacy towards information security governance. In any case, the GDPR/DPA 2016 should be considered when selecting an information security framework.
This post highlights the importance and strongly recommends that users are reminded about and understand information security policies. It is crucial that employees are aware of their duty towards information security policy compliance. With the most expensive technology, companies still have the risk that employees neglect information security policies if employees believe that information security is not their responsibility. Further recommendations towards implementing adequate and effective information security controls are to use an appropriate framework. Moreover, the controls must undergo ongoing review in regular intervals to assess their effectiveness and compliance through a maturity model.
A limitation of this post is the research papers used to create this piece. Few of the research papers selected discuss the GDPR/DPA 2016 specifically; therefore, the scope of documentation on the GDPR/DPA 2016 was limited. A further limitation of this post is that it is not sector-specific – for example towards health, financial, legal – but rather touches a little on each aspect, however due to limited resources could not go into more in-depth detail for these sectors.